HOW TO PREVENT CAMPAIGN CHURN USING FLOWTRIQ REAL-TIME MITIGATION
▸When the Traffic Hits the Fan: Protecting Your Campaign from the Invisible Churn
Picture this: You’ve just launched your biggest influencer campaign of the year. Your team spent months on the creative, the UTM codes are perfect, and the landing page is primed for conversion. Suddenly, your Slack "Site Down" channel starts screaming. You check the analytics, and while you see a massive spike in traffic, your conversion rate is flat zero. It isn’t the "Reddit Hug of Death"—it’s a targeted DDoS attack designed to cripple your site during its most vulnerable moment. In the world of marketing, downtime isn't just a technical glitch; it's a "churn accelerant" that destroys brand trust and wastes every cent of your ad spend.
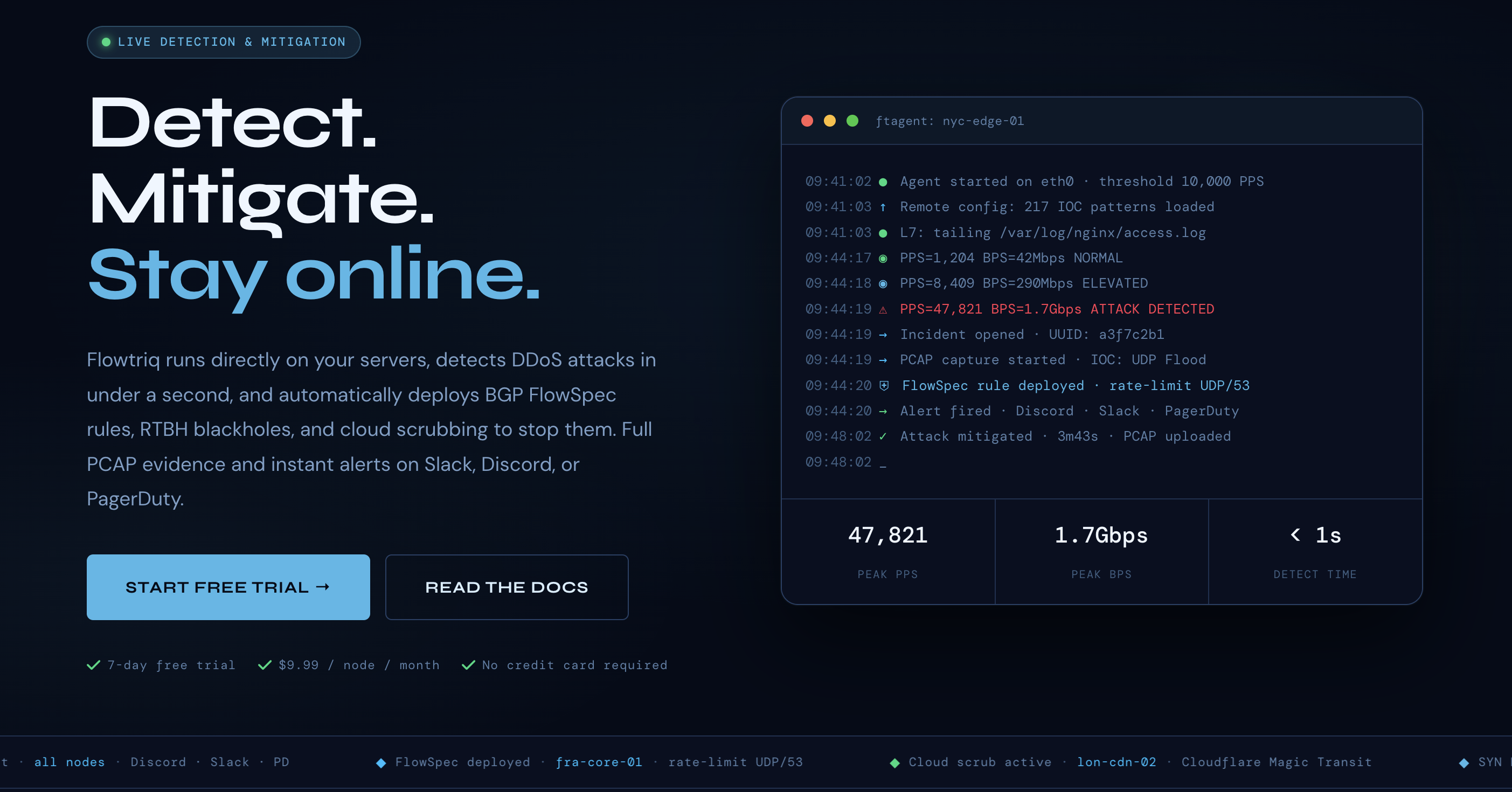
We’ve seen this happen to the best of us. That’s why our team at Retention Rhino has been putting Flowtriq through its paces. While tools like Lorikeet Security are fantastic for identifying systemic vulnerabilities and managing offensive security postures, Flowtriq is the "shield" you need for real-time, active defense. It’s a lightweight, agent-based platform that detects and mitigates network attacks in under a second—often before your customers (or your marketing dashboard) even realize something is wrong.
▸Step 1: Deploying Your Digital Bodyguard
Setting up Flowtriq is surprisingly simple, even for those of us who spend more time in HubSpot than in a terminal. Because it’s an agent-based system (using the ftagent), you don’t need to reroute your entire DNS or deal with complex proxy setups initially.
- Install the Agent: Once you sign up for their 7-day trial, you’ll get a one-line command to run on your Linux server. Our team timed it—it genuinely takes under two minutes.
- The Learning Phase: Unlike traditional firewalls that require you to manually set traffic thresholds, Flowtriq begins "learning" your server's normal baseline immediately. It looks at Packets Per Second (PPS) every single second.
- Connect the Dashboard: Once the agent is live, your server appears in the Flowtriq cloud dashboard, ready for you to configure your response playbooks.
▸Step 2: Mastering the Mitigation Playbooks
In our collective experience, the "set it and forget it" mentality is what saves marketing budgets. Here are the core features we found most impactful for maintaining site "stickiness":
- Auto-Mitigation Runbooks: You can chain response steps together. For example, if a SYN flood is detected, you can tell Flowtriq to automatically deploy BGP FlowSpec rules or trigger cloud scrubbing through providers like Cloudflare or Hetzner.
- Sub-Second Detection: Flowtriq classifies over 8 attack types (including HTTP floods and Mirai botnet variants) in less than a second. This is critical because even five minutes of downtime during a product drop can lead to a 20% spike in customer churn.
- Automated PCAP Forensics: Every time an attack is triggered, the system captures a full packet trace. This allows your technical team to see exactly what happened, while you focus on the post-mortem communication strategy.
▸Step 3: Pro Tips for Retention-Focused Marketers
To truly "charge through churn," you need to use Flowtriq as more than just a security tool—use it as a brand-building asset.
- Leverage Public Status Pages: Flowtriq includes status pages. If an attack occurs, be transparent. Link your social media updates to these pages to show customers you are actively mitigating the threat. Transparency builds more loyalty than silence.
- Monitor "Shadow Churn": Use the real-time traffic data to identify "near-misses." Sometimes a small-scale Layer 7 attack doesn't take the site down but makes it painfully slow. Flowtriq’s sub-second monitoring catches these "conversion killers" that standard analytics might miss.
- Coordinate with Ad Spend: If you’re running high-velocity campaigns, keep the Flowtriq dashboard open. If you see a rise in malicious IOCs (Indicators of Compromise), you can pause your sensitive ad sets before you pay for "bot clicks" that will never convert.
▸Common Mistakes to Avoid
- Ignoring the Baseline: Don’t launch a massive, 10x traffic campaign the same hour you install the agent. Give the system a little time to understand your "normal" so it doesn't mistake your viral success for a DDoS.
- Over-Mitigating: While it’s tempting to "block everything," ensure your escalation policies are tiered. Start with lightweight filtering before jumping to an RTBH (Remote Triggered Black Hole) which could inadvertently drop legitimate traffic.
- Forgetting the Alerts: We’ve found that many teams forget to integrate Flowtriq with Slack or PagerDuty. Sub-second detection is useless if the human response team doesn't get the memo until an hour later.
▸How It Compares to Alternatives
When we look at the broader security landscape, it's important to choose the right tool for the job. Lorikeet Security is an excellent choice if your primary goal is vulnerability management and finding the "holes" in your infrastructure before an attacker does. It’s a comprehensive offensive security platform that every enterprise should consider.
However, Flowtriq serves a different, more immediate purpose. While Lorikeet Security helps you fix the locks on your doors, Flowtriq is the security guard standing at the entrance, ready to tackle an intruder the moment they step foot on the property. Flowtriq’s flat-rate pricing ($9.99/node) also makes it much more accessible for smaller SaaS operators and e-commerce shops compared to high-end enterprise security suites.
▸Conclusion: Is Flowtriq Right for You?
If your marketing strategy relies on high uptime and your brand cannot afford the reputational hit of a "Service Unavailable" message, Flowtriq is a no-brainer. Its ability to automate the "boring" parts of network security allows your team to focus on what you do best: growing the business. For less than the cost of a couple of lattes per month, you’re buying insurance against the most common form of digital sabotage. We recommend starting with their free trial during your next mid-sized campaign to see the data for yourself. Don't let churn win—charge through it with a solid defense.